A Biased View of Risk Management Enterprise
Table of Contents9 Easy Facts About Risk Management Enterprise ShownOur Risk Management Enterprise StatementsThe Basic Principles Of Risk Management Enterprise
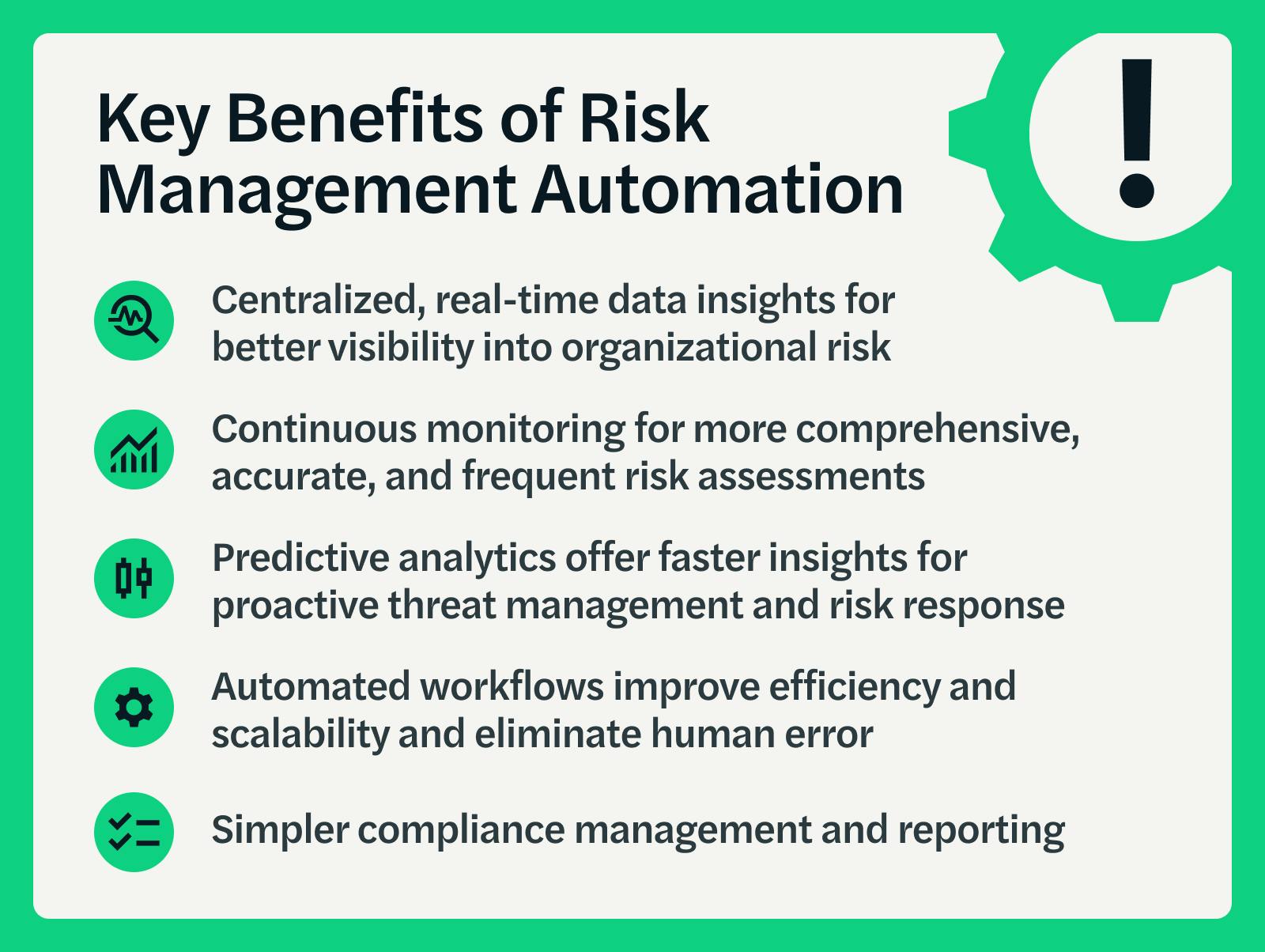
Control who can watch or edit these aspects by establishing specific gain access to civil liberties for individual customers, ensuring info protection and customized use. Allows users to tailor their user interface by picking and arranging essential data aspects. Supplies a personalized experience by allowing personalization of where and exactly how information components are presented.It allows accessibility to real-time integrated data promptly. Centers can utilize comprehensive information knowledge for quicker and much more enlightened decision-making.
Diligent is a threat monitoring software program that permits maximizing efficiency, and improves development. It likewise assists keep track of dangers with ERM software that includes incorporated analytics and adapts to your organization demands. This software program includes different helpful features. Listed below we have actually highlighted the most essential ones. So, check them out.
Getting The Risk Management Enterprise To Work
Simplifies the procedure of accumulating risk data from numerous components of the organization. Supplies management and the board with real-time threat insights. Use ACL's sophisticated analytics to detect risk patterns and predict risks.
This enables business to capture risk insights and red flags in try this web-site the third-party vendor's security report. Enables companies to record and record threat understandings and red flags in third-party vendor safety and security reports.
It also lowers threat through structured compliance and risk monitoring. It can aid gather and track all your risks in the Hyperproof threat register.
It supplies fast access to essential info and documents. This makes sure the security of Hyper evidence instances by allowing multi-factor verification (MFA) utilizing authenticator applications such as Google Authenticator, Microsoft Authenticator, or Authy.
6 Simple Techniques For Risk Management Enterprise
It provides top-tier protection functions to protect sensitive information. This threat administration software is a perfect device for facilities looking to deal with unnecessary concerns or dangers.
Individuals can visite site additionally utilize the AI-powered tools and pre-existing web content to develop, review, prioritize, and address dangers successfully. Improves the procedure of configuring and occupying threat signs up.